- Military Cac Certificates
- Dod Certificates For Mac
- Install Dod Certificates Windows 10
- Dod Cac Certificates For Mac
- Download Dod Certificates For Mac
Whenever you upgrade your operating system (OS), you will need to CAC-enable (i.e. Public Key Enable) the system all over again. You should refer to the instructions and downloads available from the web pages under Getting Started for End Users (Mac) on DISA's Information Assurance Support Environment (IASE) website. You will need middleware to use your CAC on OS X. The instructions on IASE will direct you to Smartcard Services (middleware) downloads from Mac OS forge. Smartcard Services will work for most CACs and readers, however, if you do not see your CAC keychain in the Keychain Access.app after installing the Smartcard Services package and inserting your CAC in the card reader, then I recommend using another free middleware called Centrify Express.
Military Cac Certificates
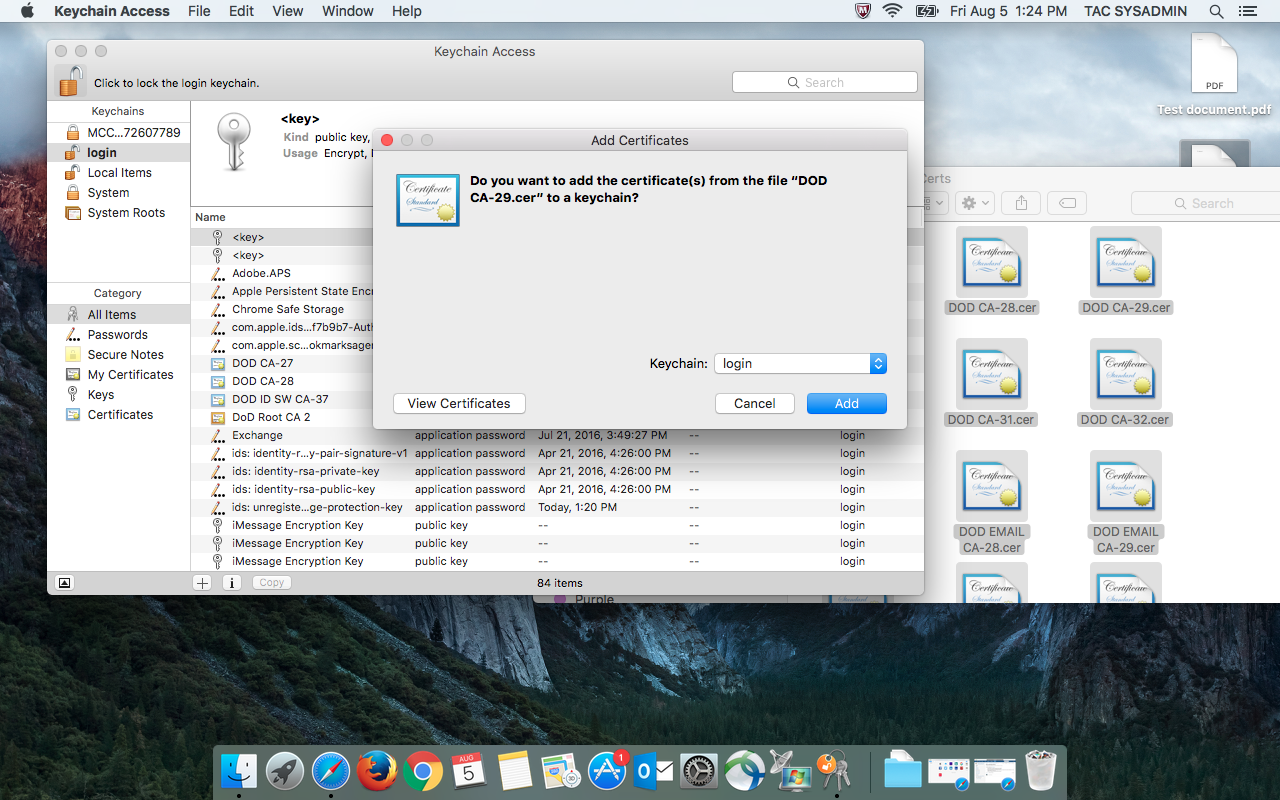
When connecting to various online services, your Mac will use certificates to validate a connection. If a certificate being used for a connection is expired or invalid, then OS X will notify you of this when attempting to use it, and offer you the choice of continuing with the connection, inspecting the certificate, or canceling the connection. Now that you have your CAC reader connected and accepted on your Mac computer, it’s time to ensure you have the right certificates in order to access DOD CAC required web pages. Procedure for Chrome and Safari Type ⇧⌘U (Shift + Command + U) to access your Utilities Find and Double click “Keychain Access”.
Aside from installing middleware, you need to download and import the DoD Root and Intermediate Certificates in your Keychain Access. Most of the DoD certificates are available if you add the 'SystemCACertificates' keychain using the File > Add Keychain option and navigating through the folders to Macintosh HD > System > Library > Keychains. You need to download and import a few certificates into the 'login' keychain, such as DOD ROOT CA 2 (3 certificates total), DOD ROOT CA 3, and any intermediate certificates that issued the certificates on your CAC, which are greater than DOD CA-30 (such as DOD CA-31, DOD EMAIL CA-31, DOD CA-32, DOD EMAIL CA-32, DOD ID CA-33, DOD EMAIL CA-33, DOD ID CA-34, DOD EMAIL CA-34, etc.). Go to the Cross-Certificate Chaining Issue page to download two zip files (i.e.Certificates_PKCS7_v4.1u4_DoD.zip and unclass-irca1_dodroot_ca2.zip, then use the File > Import Certificate option to add the certificates to the 'login' keychain. All DoD Intermediate Certificates are available for download (one-by-one) from the DoD PKI Management website at https://crl.gds.disa.mil/ (download the Certificate Authority Certificate, not the Certificate Revocation List, i.e. CRL) for each certificate.
Company: Southwest I.T. Solutions
Mar 13, 2016 9:22 PM
Please select a browser below to access instructions for configuring your browser to use the certificates on your CAC.
IE and Chrome
First check whether your certificates are already available to your browser.
For Internet Explorer 8.0 and above:
- Navigate to Tools > Internet Options > Content and click Certificates.
- On the Personal tab, review the list of certificates to determine if your CAC certificates are in the list. The certificates on your CAC will be issued by a DoD CA.
- If the certificates appear in the list, you are finished. If the certificates do not appear in the list, please see the note below.
For Google Chrome:
Dod Certificates For Mac

- Navigate to Tools > Options > Under the Hood and click Manage Certificates in the HTTPS/SSL section.
- On the Personal tab, review the list of certificates to determine if your CAC certificates are in the list. The certificates on your CAC will be issued by a DoD CA.
- If the certificates appear in the list, you are finished. If the certificates do not appear in the list, please see the note below.
NOTE: If your certificates are not in the list and you’re using ActivClient, please make sure it is installed correctly. If your certificates are not in the list and you are using other middleware, you can contact your CC/S/A for more information on the middleware requirements for your organization. You can find their contact information on our Contact Us tab.
Firefox
Below are complete instructions for using Firefox with your CAC. You may also download these instructions.
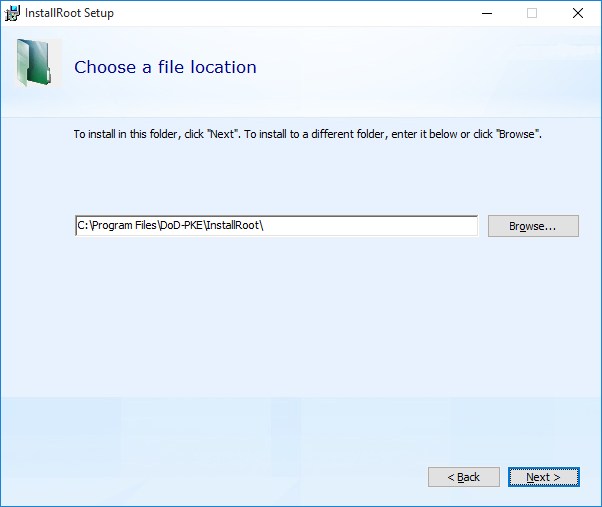
Install Certificates from InstallRoot
- Download and install the InstallRoot tool following the instructions in the InstallRoot User Guide or watch this video to learn how:
- Open the InstallRoot tool and select Firefox/Mozilla/Netscape from the Select Trust Store picklist at the bottom of the window.
- Ensure only the top Install DoD NIPRNET Certificates box is checked.
- Click the Install button and wait for the installation to complete. Please wait until you see a confirmation dialog indicating the tool is finished.
- Open Firefox
- Click on Tools > Options in the menu bar.
- In the Options window, go to Advanced > Encryption > Security Devices.
- In the new window, click on Load.
- Enter “ActivClient(CAC)” for the Module Name.
Click Browse to the right of the Module Filename field. Browse to the location of the ActivClient PKCS11 library, acpkcs211.dll. This is typically located at C:Program Files (x86)ActivIdentityActivClientacpkcs211.dll in ActivClient 6.2, and C:Windowssystem32acpkcs201-ns.dll in ActivClient 6.1 and earlier.
Click OK, and then OK again in the confirmation window.
- The confirmation message will show that the security device (CAC) was loaded. CAC certificates can now be used with the browser. Click OK to close the window.
- Open Firefox
- Click on Tools > Options in the menu bar.
- In the Options window, go to Advanced > Encryption > Validation.
- Ensure the option Use the OCSP to confirm the current validity of certificates is checked. Also ensure When an OCSP server connection fails, treat the certificate as invalid is checked.
Using Common Access Card (CAC) certificates in Firefox
These instructions will enable ActivIdentity’s ActivClient software to work within Firefox. Before proceeding, try to ensure the latest version of ActivClient is installed by going to the ActivClient website to check the latest version. Before installing the latest version, please uninstall any previous versions of ActivClient.
As of version 6.2, ActivClient by default configures Firefox to accept the CAC certificates without any additional configuration. You may use the following instructions to verify that it has been installed properly. If using an older version of ActivClient, these instructions will assist with proper configuration.
Ensure the Online Certificate Status Protocol (OCSP) is Performing Revocation Checking
With any versions of ActivClient later than 6.2, these settings will be automatically configured. However, these instructions can be used to confirm proper configuration for older versions of ActivClient.
Install Dod Certificates Windows 10

Safari
To get started you will need:
Dod Cac Certificates For Mac
- CAC (see note below)
- Card reader
You can get started using your CAC on your Mac OS X system by following these basic steps:
Download Dod Certificates For Mac
- Get a card reader
Typically Macs do not come with card readers and therefore an external card reader is necessary. At this time, the best advice for obtaining a card reader is through working with your home component. In addition, please review the DoD CAC Reader Specifications for more information regarding card reader requirements. - Download and install the OS X Smartcard Services package
The OS X Smartcard Services Package allows a Mac to read and communicate with a smart card. In order for your machine to recognize your CAC certificates and DoD websites as trusted, the installer will load the DoD CA certificates on OS X. Please refer to this page for specific installation instructions. - Address the cross-certificate chaining Issue
These instructions walk through adjusting the trust settings on the Interoperability Root CA (IRCA) > DoD Root CA 2 and the US DoD CCEB IRCA 1 > DoD Root CA 2 certificates to prevent cross-certificate chaining issues. This can make it appear that your certificates are issued by roots other than the DoD Root CA 2 and can prevent access to DoD websites. - Configure Chrome and Safari, if necessary
Safari and Google Chrome rely on Keychain Access properly recognizing your CAC certificates.- In Finder, navigate to Go > Utilities and launch KeychainAccess.app
- Verify that your CAC certificates are recognized and displayed in Keychain Access
Note: CACs are currently made of different kinds of card stock. To determine what card stock you have, look at the back of your CAC above the magnetic strip. Most CACs are supported by the Smartcard Services package, however Oberthur ID One 128 v5.5 CACs are not. Third party middleware is available that will support these CACS; two such options are Thursby Software’s PKard and Centrify’s Express for Smart Card.
